Why Penetration Testing Cloud Services Is No Longer Optional
Penetration testing cloud services is the practice of simulating real-world cyberattacks against your cloud environment to find security gaps before attackers do. Here’s a quick snapshot of what it involves and why it matters:
- What it is: Authorized, simulated attacks on your cloud infrastructure (AWS, Azure, GCP) targeting misconfigurations, weak access controls, and exposed data
- Who needs it: Any business storing data, running workloads, or using applications in the cloud
- Why now: According to Gartner, an estimated 99% of cloud breaches through 2025 result from customer misconfigurations — not provider failures
- Key benefit: Organizations that test continuously reduce their breach probability by 60-80% compared to those relying on annual audits alone
- What it covers: Identity and access management (IAM), storage permissions, APIs, serverless functions, containers, and more
The numbers are hard to ignore. Cloud infrastructure now powers 94% of enterprise workloads — yet 67% of organizations admit they don’t fully understand their own cloud attack surface. That’s a wide-open door for attackers.
And the consequences are real. The Capital One breach exposed 106 million customer records through a single misconfigured AWS firewall rule. That one oversight cost millions in fines, legal fees, and lost trust.
The good news? Most of these risks are findable — and fixable — before they become headlines.
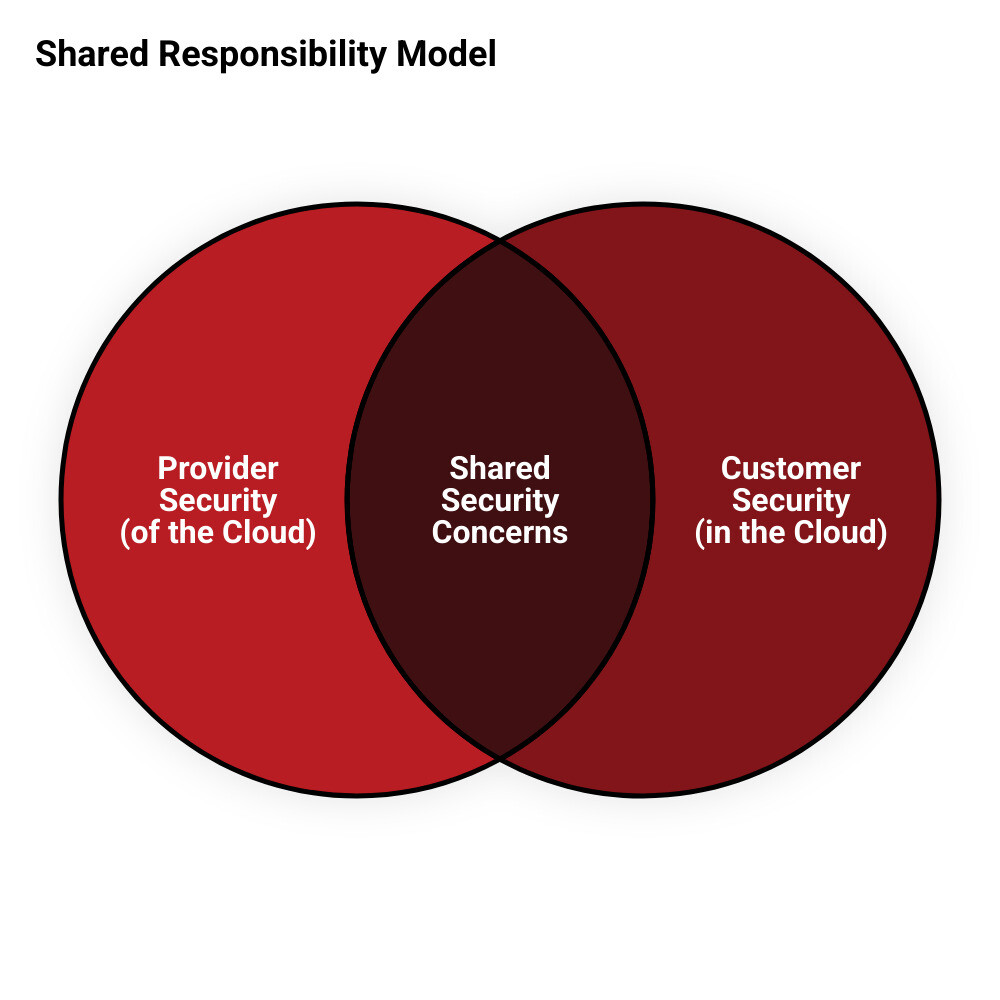
Understanding the Shared Responsibility Model in Cloud Security
One of the biggest hurdles we see at Alliance InfoSystems when talking to clients about cloud security is a simple misunderstanding: the belief that the cloud provider handles everything. While giants like Amazon, Microsoft, and Google spend billions on security, they only secure the “house”—you are still responsible for locking the doors and windows.
This is known as the Shared Responsibility Model.
- Security “of” the Cloud: This is the provider’s job. They protect the physical data centers, the hardware, and the software that runs the cloud services.
- Security “in” the Cloud: This is your job. You are responsible for your data, your configurations, and who has access to your systems.
The level of your responsibility changes depending on the service model you use. For instance, in Infrastructure as a Service (IaaS), you manage almost everything from the operating system up. In Software as a Service (SaaS), the provider does more, but you are still in charge of user permissions and data. To get a deeper look at these models, check out our guide to cloud hosting services.
To ensure you aren’t leaving gaps in your defense, the Cloud Penetration Testing Playbook from the CSA is an excellent resource for understanding where your duties end and the provider’s begin.
The Impact on Testing Scope
When we perform penetration testing cloud services, we have to be very careful about the “scope.” We focus strictly on customer-controlled systems. For example, if you have a custom virtual machine in an IaaS environment, that’s fair game for testing. However, the hypervisor (the software that runs the virtual machine) belongs to the provider and is strictly off-limits.
Testing provider-managed services requires a surgical approach. We look at how your configurations might allow an attacker to slip through, rather than trying to break the provider’s actual infrastructure. This is a critical part of any cloud migration strategy, ensuring that as you move assets, you aren’t moving vulnerabilities with them.
Multi-Cloud and Hybrid Complexities
Many of our Maryland clients use a mix of on-premises servers and multiple cloud providers. This creates “hybrid” or “multi-cloud” environments that are notoriously difficult to secure. Attackers love these setups because they can often find a weak link in an on-premises server and use it as a stepping stone to reach sensitive data in the cloud.
When penetration testing cloud services in a hybrid setup, we examine inter-cloud attack paths and how identities are synchronized between your local office and the cloud. Understanding the differences between cloud and local servers is the first step in mapping out these potential pathways.
How Penetration Testing Cloud Services Differs from Traditional Audits
If you’ve had a traditional network pentest before, you might think you know what to expect. But cloud-native testing is a different beast entirely. Traditional testing focuses on finding unpatched software or open network ports. In the cloud, the “network” is often defined by code, and the “perimeter” is your Identity and Access Management (IAM) policy.
| Feature | Traditional Pentesting | Cloud-Native Pentesting |
|---|---|---|
| Primary Focus | Network vulnerabilities & OS patches | IAM logic flaws & Misconfigurations |
| Perimeter | Firewalls and Routers | Identity (Users, Roles, Keys) |
| Assets | Static servers and hardware | Ephemeral containers and serverless functions |
| Infrastructure | Manual configuration | Infrastructure-as-Code (IaC) |
| Methodology | Port scanning and sniffing | API enumeration and token analysis |
Cloud testing requires specialized knowledge of how cloud APIs work. For a broader look at how security is evolving, see our Network Security Services Guide 2026.
Beyond Network Perimeters
In the cloud, “Identity is the new perimeter.” Attackers don’t “hack” in; they “log” in using stolen credentials or overprivileged service accounts. Penetration testing cloud services involves looking at microservices security and how an attacker might abuse a serverless function—like AWS Lambda—to gain access to your database. This is why many organizations are moving toward a managed SOC approach to keep a 24/7 eye on these complex identity movements.
The Role of Automation and AI
Cloud environments change in seconds. A developer might spin up a new database or change a firewall rule with a single line of code. This “configuration drift” means that a pentest done today might be outdated tomorrow. We utilize AI-augmented tools and continuous testing methodologies to keep up with this pace. Integrating security into your DevSecOps pipeline ensures that testing isn’t just a hurdle at the end of a project, but a constant safety net. For those who can’t manage this in-house, SOC as a Service (SOCaaS) provides the continuous oversight needed for modern cloud stacks.
The 5 Essential Phases of a Cloud Penetration Test
At Alliance InfoSystems, we follow a structured 5-phase methodology to ensure every stone is turned over. This process is part of our broader commitment to managed security.
1. Scoping and Reconnaissance for Penetration Testing Cloud Services
We start by gathering intelligence. This isn’t just about IP addresses; it’s about finding your cloud service accounts, understanding your architecture, and looking for “passive” clues. We might find leaked API keys in a public GitHub repository or discover an exposed storage bucket. This phase is about mapping the “attack surface.” For a deeper dive into how we monitor these environments, our virtual SOC guide explains the mechanics behind the scenes.
2. Vulnerability Enumeration
Once we know what you have, we look for the cracks. We use a mix of automated scanners and manual analysis to find misconfigured IAM policies, public snapshots of databases, or unencrypted storage. We don’t just look for bugs; we look for “logic flaws” in how your cloud services talk to each other.
3. Exploitation and Mission Accomplishment
This is where the “simulated attack” happens. If we find a weak IAM role, we try to “assume” it to see if we can escalate our privileges. Can we move laterally from a web server to a sensitive database? Can we exfiltrate data using legitimate cloud APIs? Techniques like token hijacking are common here, where we steal a temporary “session token” to act as a legitimate user. If we find issues, we help you with network security remediation services to close the gaps immediately.
4. Post-Exploitation
After we’ve “broken in,” we see how much damage could be done. We look for hardcoded secrets in code, check if we can access other cloud accounts linked to yours, and see if your logging and monitoring systems actually caught our activity.
5. Reporting and Remediation
A pentest is only as good as the report it generates. We provide a clear, prioritized roadmap. We don’t just give you a list of problems; we give you the business impact and step-by-step instructions on how to fix them.
Common Vulnerabilities and Provider-Specific Rules of Engagement
The statistics are startling: 78% of assessments find overprivileged IAM roles, and 63% find publicly accessible storage. These are the “low-hanging fruit” for hackers.
Navigating AWS, Azure, and GCP Penetration Testing Cloud Services Policies
You can’t just start attacking your cloud environment without knowing the rules. Each provider has a “Rules of Engagement” (RoE).
- AWS: As of 2019, AWS no longer requires pre-approval for most common services (EC2, RDS, Lambda). However, you still cannot perform Denial of Service (DoS) attacks. Check the AWS Penetration Testing policy for the full list.
- Azure: Microsoft allows pentesting but requires you to follow their specific Azure Rules of Engagement. You must not impact other customers or Microsoft’s own infrastructure.
- GCP: Google allows you to test your own projects without prior notification, provided you stay within their Acceptable Use Policy.
Following these rules is a core part of securing IT infrastructure best practices.
Cloud-Native Technology Challenges
As we move into more advanced tech, the risks change.
- Kubernetes: We look for “container escapes,” where an attacker breaks out of a single container to take control of the entire server cluster.
- Serverless (Lambda/Functions): We watch for “Denial of Wallet” attacks. Instead of crashing your site, an attacker triggers your serverless functions millions of times, sticking you with a massive bill.
- Infrastructure-as-Code (IaC): If your Terraform or CloudFormation templates have a security flaw, you’ll deploy that flaw every time you update your site.
These are the unique hurdles of cloud virtualization.
Compliance and Business Value: Beyond the Technical Report
For many Maryland businesses, penetration testing cloud services isn’t just about security—it’s about staying in business. Regulations like HIPAA (for healthcare) or PCI DSS (for credit cards) now have strict requirements for cloud environments.
Demonstrating ROI to Executives
How do you explain the cost of a pentest to your CEO?
- Breach Prevention: The average cost of a cloud breach is $4.45 million. A pentest is a tiny fraction of that.
- Customer Trust: If you handle data for other companies, they will likely ask for your latest pentest report before signing a contract.
- Audit Efficiency: Having a clean pentest report makes your SOC 2 or ISO 27001 audit go much faster. Working with a SOC 2 certified MSP can further streamline this process.
Effective network security management proves its value by preventing the “big one” that could sink the company.
Real-World Lessons from Cloud Breaches
We’ve already mentioned Capital One, but they aren’t alone. Countless companies have left S3 buckets “public,” exposing millions of customer records. Others have had their cloud “keys” stolen from developer laptops, allowing attackers to clone entire databases in minutes. These are the modern cyber threats that a proper pentest is designed to catch.
Frequently Asked Questions about Cloud Pentesting
Do I need permission from my cloud provider to conduct a pentest?
Generally, no for the major services on AWS and GCP. Azure allows it within specific guidelines. However, you must always avoid “out of scope” infrastructure like the provider’s underlying physical network or hardware. Always consult the latest Rules of Engagement for your specific provider to ensure you don’t violate your service agreement.
How often should organizations conduct cloud penetration testing?
Because cloud environments are so dynamic, an annual test is rarely enough. We recommend quarterly testing as a baseline for most businesses. If you are in a high-risk industry or have a “continuous deployment” cycle where code changes daily, you should consider monthly or even continuous automated testing.
What are the most common findings in cloud security assessments?
The “Big Three” are:
- Overprivileged IAM Roles: Giving a user “Admin” rights when they only need to read one file.
- Publicly Accessible Storage: Leaving S3 buckets or Azure Blobs open to the entire internet.
- Weak Logging: Not having a record of who accessed what, which makes it impossible to investigate a breach after it happens.
Conclusion
At Alliance InfoSystems, we understand that moving to the cloud is a big step, and keeping it secure can feel overwhelming. With over 20 years of experience serving the Maryland area, we specialize in providing flexible, customized security solutions that fit your specific business needs.
We don’t believe in one-size-fits-all security. Whether you are just starting your cloud journey or looking to harden a complex multi-cloud environment, our team is here to help you navigate penetration testing cloud services with confidence.
Ready to see where your cloud gaps are? Secure your environment with our Cloud Virtualization Services today.