What Is Cyber Security in Companies (And Why It Can’t Wait)
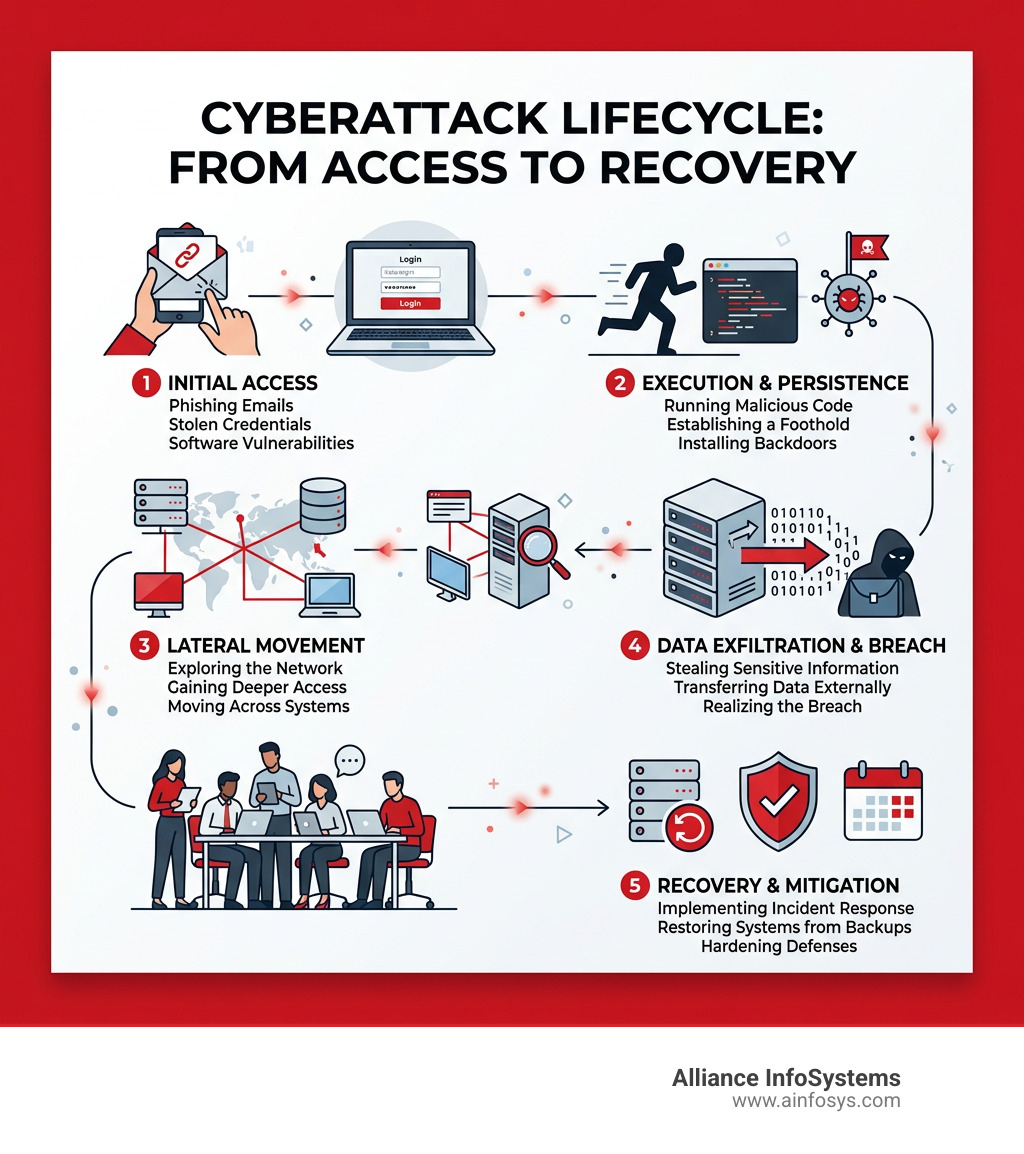
Cyber security in companies is the practice of protecting business systems, networks, and data from digital attacks, unauthorized access, and damage — covering three core actions: prevention, detection, and response.
Here’s a quick summary of what that means in practice:
- Prevention — stopping threats before they cause harm (firewalls, strong passwords, software updates)
- Detection — identifying threats that get through (monitoring, alerts, anomaly detection)
- Response — containing damage and recovering fast (incident response plans, backups, forensics)
Every business that uses the internet has something cybercriminals want — customer data, payment information, or access to larger networks. And the threat is growing fast. Organizations faced an average of 1,876 cyberattacks per week in just the third quarter of 2024 alone — a 75% jump from the year before.
The consequences are real. A single breach can mean:
- Financial losses from ransomware payments, legal fees, and lost business
- Reputation damage that drives customers away
- Operational shutdowns that can last days or weeks
And yet many businesses — especially small and mid-sized ones — are still operating without a solid plan.
No business is too small to be a target. Cybercriminals are opportunists. They go after whoever is easiest to breach, not just the biggest companies.
I’m Sara Szot, President of Alliance InfoSystems, and I’ve seen how the right approach to cyber security in companies can mean the difference between a minor incident and a business-ending event. This guide brings together everything you need to protect your business — clearly and without the jargon.
The Evolving Landscape of Cyber Security in Companies
The digital world isn’t what it was even five years ago. Today, we aren’t just defending against a lone hacker in a basement; we are facing organized, well-funded criminal enterprises and even state-sponsored actors. The statistics are sobering: 72% of organizations report a rise in cyber threats, and the sheer volume of attacks—averaging 1,876 per week per organization—shows that the “it won’t happen to me” mentality is a dangerous gamble.
Why is the landscape shifting so violently? A few factors are at play. First, there is the rapid adoption of AI. While we use AI to improve our businesses, 90% of companies lack the maturity to counter today’s AI-enabled threats. Attackers are using generative AI to create more convincing phishing emails and adaptive malware that can sniff out weaknesses in real-time.
Geopolitical tensions also play a role. When global conflicts flare up, cyber warfare often follows, and private companies—especially those in critical infrastructure or defense supply chains—frequently find themselves in the crosshairs. This is why it’s vital to ask yourself: Are You at Risk of a Cyberattack? Usually, the answer is a resounding “yes.”
According to the State of Cybersecurity Report 2023, only 10% of organizations currently occupy what we call the “Reinvention-Ready Zone.” These are the companies that have successfully integrated their cyber strategy with their overall business goals. They aren’t just buying software; they are building resilience.
Modern Threats: From Ransomware 2.0 to Social Engineering
The “bad guys” have upgraded their toolkit. We used to worry about basic viruses; now we deal with “Ransomware 2.0.” In the old days, a hacker would encrypt your files and ask for money to unlock them. Today, they use “double extortion.” They steal your sensitive data first, then encrypt your systems. If you refuse to pay the ransom, they threaten to leak your private customer information or trade secrets to the public.
Ransomware was present in 44% of breaches recently analyzed, and it hits small businesses particularly hard. In fact, 88% of breaches in SMBs involved ransomware compared to just 39% in large organizations. This is why knowing 7 Ways to Avoid Ransomware in Your Business is no longer optional—it’s a survival skill.
Then there is the “human element.” Phishing remains the most common entry point for attackers. These aren’t just poorly spelled emails anymore; they are sophisticated messages that look exactly like they came from your bank or even your own CEO. Learning How to Stop Phishing Emails involves both better technology and better employee training.
We also have to watch out for:
- Supply Chain Attacks: Attackers target your vendors or software providers to get to you. If your partner is weak, you are vulnerable.
- Insider Threats: Sometimes the threat comes from within—whether it’s a disgruntled employee or just someone making a careless mistake.
- Social Engineering: This is the art of manipulation. Attackers might call your help desk pretending to be an executive who “forgot their password.” You can Read more about social engineering tactics to see just how creative these scammers can be.
Critical Components of a Corporate Defense Strategy
Building a “Corporate Shield” requires more than just installing an antivirus and hoping for the best. It requires a layered approach. We often talk about three different types of assessments that help us understand where we stand:
| Assessment Type | What it Does | When You Need It |
|---|---|---|
| Vulnerability Assessment | Uses automated tools to find technical flaws and unpatched software. | Monthly or quarterly as a baseline. |
| Penetration Testing | A “white hat” hacker tries to actually break in to test your defenses. | Annually or after major network changes. |
| Risk Assessment | A holistic look at how a breach would impact your business (PR, legal, financial). | When building or updating your long-term strategy. |
One of the most effective modern strategies is Zero Trust. The old way of thinking was “trust but verify.” Zero Trust flips that on its head: “Never trust, always verify.” It assumes that the threat could already be inside the network. This involves strict Identity security and device posture checks to ensure that only the right people, on the right devices, can access sensitive data.
Other critical pieces include:
- Data Encryption: Making sure your data is unreadable if it is stolen.
- Network Segmentation: Dividing your network into sections so that if one part is breached, the attacker can’t easily move to the rest of the company.
- Incident Response: Having a “fire drill” plan ready so everyone knows what to do the second a breach is detected. For more details, check out How to Secure IT Infrastructure Best Practices.
Implementing Basic Hygiene for Cyber Security in Companies
Think of cyber hygiene like washing your hands—it’s simple, but it prevents the vast majority of “infections.” If every company followed these Top 10 Cyber Security Practices, the success rate of cyberattacks would plummet.
- Multi-Factor Authentication (MFA): This is the single most important step you can take. Even if a hacker steals a password, they can’t get in without that second code on your phone.
- Strong Access Management: Use the “principle of least privilege.” Employees should only have access to the data they absolutely need to do their jobs. You can learn more about access management to see how this works in practice.
- Password Health: Stop using “Password123.” Use long, complex phrases or a password manager. Curious about your own? Check How Secure is My Password?.
- Software Patching: When your computer says it needs an update, do it! Most updates are actually security patches for “holes” that hackers have already discovered.
Emerging Technologies Reshaping Cyber Security in Companies
As threats evolve, so do our tools. We are now seeing a massive shift toward Automation. In the past, a security analyst had to manually look at every alert. Today, 89% of “Cyber Transformers”—the top-performing companies—rely heavily on automation to triage threats.
Generative AI is a double-edged sword. While hackers use it, we use it to find patterns in billions of data points that a human would miss. We also see the rise of XDR (Extended Detection and Response), which integrates security across your entire “stack”—email, servers, cloud, and endpoints—giving us a bird’s-eye view of everything happening in your environment.
Cloud security is also becoming more critical as more Maryland businesses move their operations to the cloud. It’s not just about “the cloud” being secure; it’s about how you configure it. Finally, we are keeping an eye on Quantum Computing. While it’s still in the early stages, it has the potential to break current encryption, so “post-quantum” security is already being discussed in high-level circles. If you want to Stop ransomware in its tracks, you need to stay ahead of these technological curves.
The Human Firewall and Career Growth
You can have the most expensive firewall in the world, but if an employee clicks a malicious link in an email, the door is wide open. That’s why we call your staff the “Human Firewall.”
Training isn’t just a “check the box” activity. It’s about building a culture where people feel comfortable reporting a suspicious email rather than feeling embarrassed that they clicked it. We recommend at least 5 Ways to Keep Employees More Cyber Aware, including simulated phishing tests and regular “lunch and learn” sessions.
Because the need for protection is so high, the job market is exploding. There are currently an estimated 4.8 million unfilled cybersecurity positions worldwide. For those looking to join the field, the prospects are bright:
- Security analysts earn a median salary of $124,910 per year, with 29% growth expected over the next decade.
- Security engineers and architects often earn even more, with roles becoming increasingly specialized.
If you’re interested in making a career change, many institutions allow you to Apply online for cybersecurity degrees to get the foundational knowledge needed to protect the corporate world.
Small Business Protection and Regulatory Compliance
If you are a small business in Maryland, you might think you aren’t a target. But if you work with the Department of Defense (DoD) or other federal agencies, you are a major target. Cybercriminals often try to enter the “big” government networks through the “small” vendors that supply them.
This has led to strict DoD contract requirements like the Cybersecurity Maturity Model Certification (CMMC). To win or keep these contracts, you must prove you can protect:
- Federal Contract Information (FCI): Information provided by the government that isn’t intended for public release.
- Controlled Unclassified Information (CUI): Sensitive information that requires safeguarding but isn’t “classified.”
Meeting these standards can be daunting for a small team. We suggest starting with the 10 Cyber Security Tips for Small Business provided by the FCC. You can also utilize free resources like the Global Cyber Alliance’s toolkit to begin your journey toward compliance and safety.
Frequently Asked Questions about Corporate Cybersecurity
Why is cybersecurity essential for companies of all sizes?
Cybersecurity is essential because every business now relies on digital data. Whether it’s your customer list, your proprietary designs, or your financial records, that data has value. Small businesses are often used as “stepping stones” to get to larger partners, and a single breach can cause enough financial and reputation damage to force a small company to close its doors permanently.
What are the most common cyber threats facing businesses today?
The “Big Three” are phishing, ransomware, and social engineering. Phishing tricks employees into giving up credentials; ransomware locks your data for extortion; and social engineering uses psychological manipulation to bypass technical security. We are also seeing a massive rise in supply chain attacks, where hackers target your software providers to gain access to your systems.
How does AI adoption reshape cyber risks for businesses?
AI is a double-edged sword. It allows attackers to automate their efforts, creating millions of unique phishing emails and malware variants that traditional antivirus software can’t recognize. However, it also allows defenders to analyze massive amounts of network traffic to spot tiny anomalies that indicate a breach is in progress. The risk lies in the “maturity gap”—most companies are adopting AI for productivity faster than they are adopting it for security.
Conclusion
At Alliance InfoSystems, we’ve spent over 20 years helping Maryland-based companies navigate these complex waters. We know that there is no “one-size-fits-all” solution for cyber security in companies. A small medical practice in Baltimore has different needs than a defense contractor in Bethesda.
Our mission since 2004 has been to provide flexible, customized, and cost-efficient IT management and security solutions. We don’t just sell you software; we become your partner in building a resilient “Corporate Shield.” Whether you need a full-scale risk assessment or are looking for Managed Security Services to take the burden off your internal team, we are here to help.
Don’t wait for a weekly attack to become a permanent disaster. Let’s work together to make your business “Reinvention-Ready” and secure for the future.